Intelligent Healthcare with Azure Bring Your Own Key (BYOK) technology
Sensitive health data processed by hospitals and insurers is under constant attack from malicious actors who try to gain access to health care systems with the goal to steal or extort personal health information. Change Healthcare has implemented a Bring Your Own Key (BYOK) solution based on Microsoft Azure Cloud services and introduces Intelligent Healthcare today.
Change Healthcare is enabling payers and providers to have immediate and granular control over their data by transferring the ownership of encryption keys used to encrypt data at rest. This allows Change Healthcare customers to make security changes without involvement by Change Healthcare personnel and have their cloud-based systems re-encrypted and operational without service interruptions. The BYOK management capabilities include revoking access to encryption keys and rotating or deleting encryption keys on demand and at the time of a potential compromise.
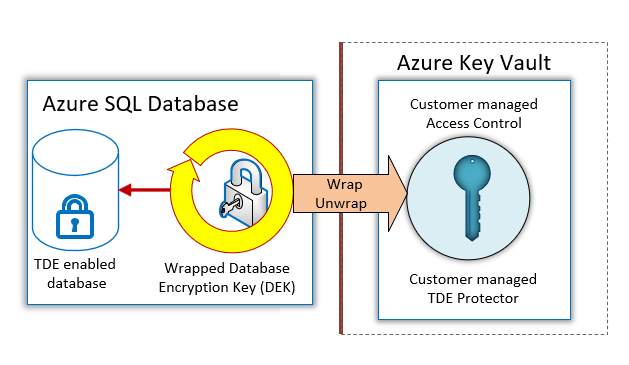
For the Intelligent Healthcare solution, Change Healthcare implemented Azure SQL Database Transparent Data Encryption (TDE) with BYOK support. TDE with BYOK encrypts databases, log files and backups when written to disk, which protects data at rest from unauthorized access. TDE with BYOK support integrates with Azure Key Vault, which provides highly available and scalable secure storage for RSA cryptographic keys backed by FIPS 140-2 Level 2 validated Hardware Security Modules (HSMs). Key Vault streamlines the key management process and enables customers to maintain full control of encryption keys and allows them to manage and audit key access.
Customers can generate and import their RSA key to Azure Key Vault and use it with Azure SQL Database and Azure SQL Data Warehouse TDE with BYOK support. Azure SQL Database handles the encryption and decryption of data stored in databases, log files, and backups in a fully transparent fashion by using a symmetric Database Encryption Key (DEK), which is in turn protected with the customer managed key called TDE Protector stored in the customer owned Azure Key Vault.
Taking advantage of BYOKs, customers gain more control over their data and can create, rotate and delete encryption keys, as well as grant and revoke key vault access to Azure SQL Database at any time. Revoking access in Azure Key Vault will effectively block access to all databases when the TDE Protector is inaccessible by Azure SQL Database. A SQL Database that doesn’t have access to the TDE Protector cannot get loaded into memory and a live database that loses access to Azure Key Vault or the TDE Protector will go offline within 24 hours.
Overview of TDE with customer managed keys and Azure Key Vault integration:
Source: Big Data