Advanced Threat Protection for Azure Database for PostgreSQL in preview
This blog post was co-authored by Ron Matchoro, Principal Program Manager, Azure SQL Database.
Advanced Threat Protection detects anomalous database activities indicating potential security threats to Azure Database for PostgreSQL.
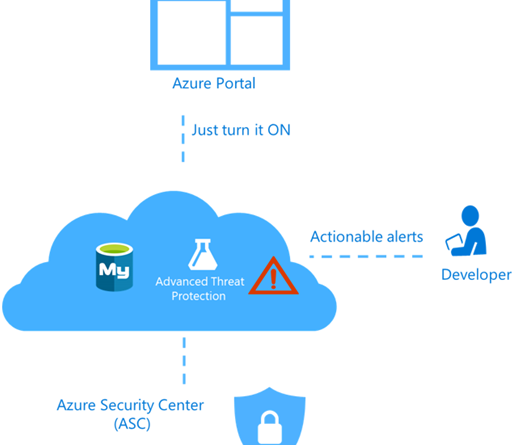
Advanced Threat Protection provides a new layer of security, which enables customers to detect and respond to potential threats as they occur by providing security alerts on anomalous database activities. Advanced Threat Protection makes it simple to address potential threats to the Azure Database for PostgreSQL server and integrates its alerts with Azure Security Center, without needing to be a security expert.
For a full investigative experience, it is recommended to use Server Logs in Azure Database for PostgreSQL, which generates database query and error logs.
The benefits of Advanced Threat Protection include:
- Simple configuration of Advanced Threat Protection policy via the Azure portal.
- Clear email alerts upon detection of suspicious database activities.
- Ability to explore the activity log around the time of the event using the Azure portal.
- No need to modify database procedures or application code.
Set up Advanced Threat Protection for your Azure Database for PostgreSQL server in the Azure portal
- Launch the Azure portal.
- Navigate to the configuration page of the Azure Database for PostgreSQL server you want to protect. In the Settings page, select Advanced Threat Protection.
- In the Advanced Threat Protection configuration blade:
- Turn ON Threat detection.
- Configure the list of emails that will receive security alerts upon detection of anomalous database activities.
- Click Save in the Advanced Threat Protection configuration blade to save the new or updated threat detection policy.
Explore anomalous PostgreSQL server activities upon detection of a suspicious event
You will receive an email notification upon detection of anomalous database activities. The email will provide information about the suspicious security event including the nature of the anomalous activities, database name, server name, and the event time. In addition, it will provide information on possible causes and provide recommended actions to investigate and mitigate the potential threat to the Azure Database for PostgreSQL server.
Clicking on the view recent alerts link in the email will launch the Azure portal and show the Azure Security Center alerts blade, which provides an overview of active SQL threats detected on the Azure Database for PostgreSQL server.
Clicking on a specific alert provides additional details and actions for investigating this threat and remediating future threats.
Azure Database for PostgreSQL server Advanced Threat Protection alerts
Advanced Threat Detection for Azure Database for PostgreSQL server detects anomalous activities indicating unusual and potentially harmful attempts to access or exploit databases. It can trigger the following alerts:
- Access from unusual locations: This alert is triggered when there is a change in the access pattern to an Azure Database for PostgreSQL server, where someone has logged onto the Azure Database for PostgreSQL server from an unusual geographical location. In some cases, the alert detects a legitimate action, meaning a new application or developer’s maintenance operation. In other cases, the alert detects a malicious action such as former employee, external attacker, etc..
- Access from unusual Azure data center: This alert is triggered when there is a change in the access pattern to Azure Database for PostgreSQL server. Where someone has logged onto the Azure Database for PostgreSQL server from a Azure Data Center that was not seen accessing this Managed Instance during the recent period. In some cases, the alert detects a legitimate action such as your new application in Azure, Power BI, Azure SQL Query Editor, etc. In other cases, the alert detects a malicious action from an Azure resource or service such as a former employee or external attacker.
- Access from unfamiliar principal: This alert is triggered when there is a change in the access pattern to Azure Database for PostgreSQL server, where someone has logged on to the Azure Database for PostgreSQL server using an unusual principal. In some cases, the alert detects a legitimate action such as new application developer’s maintenance operation. In other cases, the alert detects a malicious action such as a former employee or external attacker.
- Access from a potentially harmful application: This alert is triggered when a potentially harmful application is used to access the database. In some cases, the alert detects penetration testing in action. In other cases, the alert detects an attack using common attack tools.
- Brute force login credentials: This alert is triggered when there is an abnormally high number of failed logins with different credentials. In some cases, the alert detects penetration testing in action. In other cases, the alert detects a brute force attack.
Next steps
- Learn more about Advanced Threat Protection for Azure Database for PostgreSQL.
- Visit the pricing page for Advanced Threat Protection for Azure Database for PostgreSQL
Source: Azure Blog Feed