Automate your attack response with Azure DDoS Protection solution for Microsoft Sentinel
DDoS attacks are most known for their ability to take down applications and websites by overwhelming servers and infrastructure with large amounts of traffic. However, there are additional objectives for cybercriminals to use DDoS attacks to exfiltrate data, extort, act politically, or ideologically. One of the most devastating features of DDoS attacks is their unique ability to disrupt and create chaos in targeted organizations or systems. This plays well for bad actors that leverage DDoS as smokescreen for more sophisticated attacks, such as data theft. This demonstrates the increasingly sophisticated tactics cybercriminals use to intertwine multiple attack vectors to achieve their goals.
Azure offers several network security products that help organizations protect their applications: Azure DDoS Protection, Azure Firewall, and Azure Web Application Firewall (WAF). Customers deploy and configure each of these services separately to enhance the security posture of their protected environment and application in Azure. Each product has a unique set of capabilities to address specific attack vectors, but the most benefit speaks to the power of relationship—when combined these three products provide more comprehensive protection. Indeed, to combat modern attack campaigns one should use a suite of products and correlate security signals from one to another, to be able to detect and block multi-vector attacks.
We are announcing a new Azure DDoS Protection Solution for Microsoft Sentinel. It allows customers to identify bad actors from Azure’s DDoS security signals and block possible new attack vectors in other security products, such as Azure Firewall.
Using Microsoft Sentinel as the glue for attack remediation
Each of Azure’s network security services is fully integrated with Microsoft Sentinel, a cloud-native security information and event management (SIEM) solution. However, the real power of Sentinel is in collecting security signals from these separate security services and analyzing them to create a centralized view of the attack landscape. Sentinel correlates events and creates incidents when anomalies are detected. It then automates the response to mitigate sophisticated attacks.
In our example case, when cybercriminals use DDoS attacks as smokescreen to data theft, Sentinel detects the DDoS attack, and uses the information it gathers on attack sources to prevent the next phases of the adversary lifecycle. By using remediation capabilities in Azure Firewall and other network security services in the future, the attacking DDoS sources are blocked. This cross-product detection and remediation magnifies the security posture of the organization, where Sentinel is the orchestrator.
Automated detection and remediation of sophisticated attacks
Our new Azure DDoS Protection Solution for Sentinel provides a single consumable solution package that allows customers to achieve this level of automated detection and remediation. The solution includes the following components:
- Azure DDoS Protection data connector and workbook.
- Alert rules that help retrieve the source DDoS attackers. These are new rules we created specifically for this solution. These rules may be utilized by customers to achieve other objectives for their security strategy.
- A Remediation IP Playbook that automatically creates remediation in Azure Firewall to block the source DDoS attackers. Although we document and demonstrate how to use Azure Firewall for remediation, any 3rd party firewall that has a Sentinel Playbook can be used for remediation. This provides the flexibility for customers to use this new DDoS solution with any firewall.
The solution is initially released for Azure Firewall (or any third-party firewall), and we plan to enhance it to support Azure WAF soon.
Let’s see a couple of use cases for this cross-product attack remediation.
Use case #1: remediation with Azure Firewall
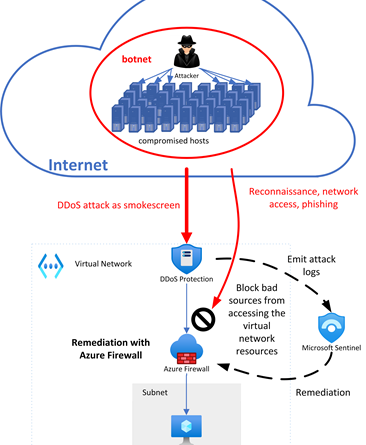
Let’s consider an organization that use Azure DDoS Protection and Azure Firewall, and consider the attack scenario in the following figure:
An adversary controls a compromised bot. They starts with a DDoS smokescreen attack, targeting the resources in the virtual network for that organization. They then plan to access the network resources by scanning and phishing attempts until they’re able to gain access to sensitive data.
Azure DDoS Protection detects the smokescreen attack and mitigates this volumetric network flood. In parallel it starts sending log signals to Sentinel. Next, Sentinel retrieves the attacking IP addresses from the logs, and deploys remediation rules in Azure Firewall. These rules will prevent any non-DDoS attack from reaching the resources in the virtual network, even after the DDoS attacks ends, and DDoS mitigation ceases.
Use case #2: remediation with Azure WAF (coming soon)
Now, let’s consider another organization who runs a web application in Azure. It uses Azure DDoS Protection and Azure WAF to protect its web application. The adversary objective in this case is to attack the web application and exfiltrate sensitive data by starting with a DDoS smokescreen attack, and then launch web attacks on the application.
When Azure DDoS Protection service detects the volumetric smokescreen attack, it starts mitigating it, and signals logs to Sentinel. Sentinel retrieves the attack sources and applies remediation in Azure WAF to block future web attacks on the application.
Get started with Azure DDoS protection today
As attackers employ advanced multi-vector attack techniques during the adversary lifecycle, it’s important to harness security services as much as possible to automatically orchestrate attack detection and mitigation.
For this reason, we created the new Azure DDoS Protection solution for Microsoft Sentinel that helps organizations to protect their resources and applications better against these advanced attacks. We will continue to enhance this solution and add more security services and use cases.
Follow our step-by-step configuration guidance on how to deploy the new solution.
Source: Azure Blog Feed